Empowering Tanzanian Farmers: Wakandi and TCDC's New SACCOS Initiative
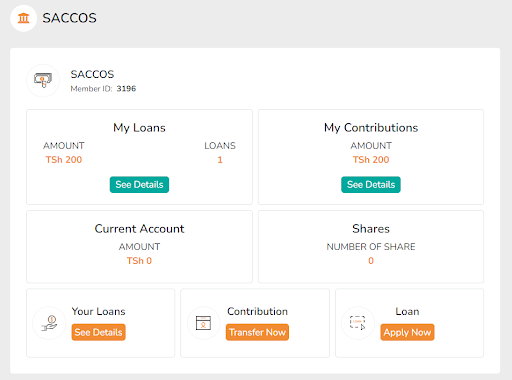
On 10th July 2025, Wakandi Tanzania Limited, in collaboration with the Tanzania Cooperative Development Commission (TCDC) and the Tanzania Federation of Cooperatives (TFC), launched a transformative...